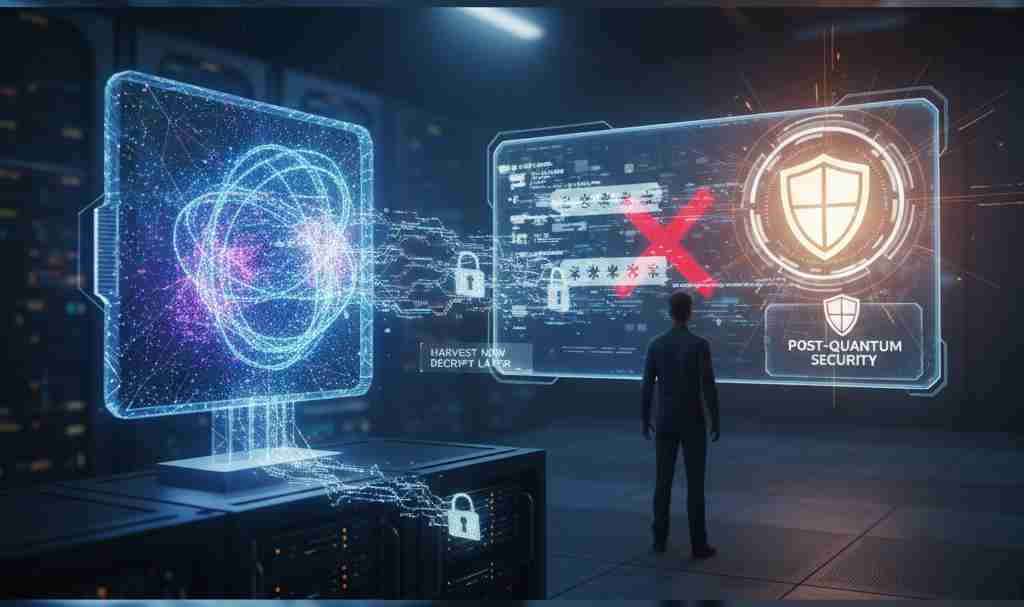
I need to tell you something that might freak you out a little: there are people right now storing encrypted data they can’t read, just waiting for quantum computers to become powerful enough to crack it.
It’s called “harvest now, decrypt later.” And it’s not science fiction – it’s happening.
Let me explain what quantum computing is, why it matters for cybersecurity, and what you need to know before your bank account becomes someone’s science project.
What Is Quantum Computing Anyway?
Okay, forget the physics for a second. Let me explain this in a way that actually makes sense.
Your regular computer (your laptop, your phone) processes information using bits. Each bit is either a 0 or a 1. Like a light switch – it’s either on or off.
Quantum computers use quantum bits, or “qubits.” Here’s where it gets weird: a qubit can be 0, 1, or both at the same time. It’s like Schrödinger’s cat for data – it exists in multiple states simultaneously until you measure it.
This sounds like meaningless physics mumbo jumbo until you understand what it means in practice: quantum computers can process massive amounts of possibilities at once instead of checking them one by one.
Imagine trying every key on a keyring to unlock a door. A regular computer tries one key at a time. A quantum computer tries them all simultaneously. That’s the basic idea.
Why Should You Care?
Here’s the thing: most of the security that protects your online life – your banking, your emails, your private messages – relies on encryption that’s basically impossible for regular computers to crack.
The math works like this: it would take a traditional supercomputer thousands of years to break modern encryption. So we feel safe.
But a sufficiently powerful quantum computer? It could crack that same encryption in hours or days. Maybe minutes.
Everything you think is secure might not be secure anymore. And we’re not talking about some distant future. We’re talking about the next 5-10 years. Some experts say sooner.
The Encryption Problem
Let me break down exactly why this is terrifying:
RSA Encryption
This is what protects most of your internet traffic right now. When you see that little padlock in your browser, you’re probably using RSA encryption.
RSA works because factoring large numbers is really, really hard for classical computers. It’s based on mathematical problems that take forever to solve by brute force.
Quantum computers? They’re built to solve exactly these kinds of problems. There’s literally an algorithm called Shor’s algorithm that could break RSA encryption once quantum computers are powerful enough.
The Timeline
We don’t have quantum computers powerful enough to break encryption yet. But we’re getting close. Some experts think we’re 5-10 years away. Others think it could happen sooner.
Here’s why that’s a problem: data stolen today is still valuable in 10 years. Medical records, financial information, government secrets, intellectual property – if someone steals it now and decrypts it in 2030, the damage is the same.
That’s the “harvest now, decrypt later” attack I mentioned. Foreign governments and sophisticated criminals are already doing this. They’re collecting encrypted data they can’t read yet, betting on quantum computers becoming available before the data becomes worthless.
Real-World Impact
Let’s talk about what this actually means for different groups:
For Individuals
Your personal data is probably not a target for quantum decryption. The NSA isn’t going to use a multi-billion dollar quantum computer to read your emails.
But if you’re involved in anything sensitive – government work, defense contracting, high-level corporate stuff – you should care. A lot.
Also, consider this: financial institutions, healthcare providers, and tech companies store your data. If their encryption gets broken, your information becomes vulnerable. You might not be the target, but you could be collateral damage.
For Businesses
This is where things get serious. Trade secrets, intellectual property, merger plans, financial data – everything you’re encrypting now could be readable in a few years.
If you’re in pharmaceuticals, defense, finance, or tech, you need a quantum-safe encryption strategy. Not eventually. Now.
The companies that figure this out early will have a competitive advantage. The ones that wait? They’ll be scrambling to respond after a breach.
For Governments
National security depends on encryption. Military communications, intelligence operations, diplomatic cables – all encrypted with systems that quantum computers could break.
This is why governments worldwide are investing billions in quantum computing research. It’s both an offensive and defensive priority. Break the enemy’s encryption while protecting your own.
What’s Being Done About It
The good news: smart people saw this coming and have been working on solutions.
Post-Quantum Cryptography
This is encryption designed to resist quantum computer attacks. It uses different mathematical problems that even quantum computers struggle with.
The National Institute of Standards and Technology (NIST) has been running a competition to develop and standardize post-quantum encryption algorithms. In 2024, they announced the first set of approved algorithms.
This is huge. It means we have encryption methods that should work even in a quantum computing world.
The Migration Challenge
Here’s the problem: switching from current encryption to quantum-safe encryption is a massive undertaking.
Every system, every protocol, every piece of software that uses encryption needs to be updated. This isn’t a simple software patch. It’s a fundamental overhaul of how digital security works.
And it needs to happen before quantum computers become powerful enough to break current encryption. We’re in a race against time.
Quantum Key Distribution
There’s another approach: quantum key distribution (QKD). This uses the principles of quantum mechanics to create unhackable communication channels.
Any attempt to intercept the communication disturbs the quantum state and gets detected. It’s theoretically perfect security.
The catch? It’s expensive, requires special hardware, and only works over limited distances. It’s great for government and military applications but not practical for everyday use yet.
What Quantum Computers Can Actually Do
Let’s zoom out from security for a second and talk about what makes quantum computers special beyond breaking encryption:
Drug Discovery
Simulating molecular interactions is incredibly complex. Quantum computers could model how drugs interact with the body at a molecular level, dramatically speeding up drug development.
We’re talking about potentially curing diseases faster and designing personalized medicine based on individual genetics.
Financial Modeling
Risk analysis, portfolio optimization, fraud detection – these involve analyzing massive amounts of variables and possibilities. Quantum computers excel at this.
The finance industry is betting big on quantum computing because whoever gets it working first will have an enormous advantage in markets.
Artificial Intelligence
Machine learning involves processing huge datasets and finding patterns. Quantum computers could supercharge AI development, leading to smarter, faster, more capable AI systems.
The combination of quantum computing and AI could be transformative. Or terrifying. Possibly both.
Climate Modeling
Understanding and predicting climate change requires processing incomprehensible amounts of data and running complex simulations. Quantum computers could help us better understand climate patterns and develop solutions.
Optimization Problems
Logistics, supply chain management, traffic flow, energy grid management – these are all optimization problems that quantum computers could solve more efficiently.
Imagine city traffic systems that actually work, or supply chains that never have bottlenecks. That’s the potential.
The Current State of Quantum Computing
Where are we actually at with this technology? The truth is: early stages, but progressing fast.
What We Have Now
Companies like IBM, Google, and others have working quantum computers. But they’re limited:
- Small number of qubits (dozens to hundreds, not millions)
- High error rates (qubits are fragile and easily disrupted)
- Require extreme conditions (near absolute zero temperatures)
- Expensive and complex to operate
These are prototype systems. They can do some things regular computers can’t, but they’re not ready to break your encryption yet.
The Progress
The number of qubits in quantum computers has been growing exponentially. Error rates are decreasing. New approaches to quantum computing are being developed.
We’re at a similar stage to where classical computers were in the 1950s – clunky, expensive, limited, but with obvious potential.
The Challenges
Making quantum computers practical faces huge obstacles:
Decoherence: Qubits are extremely fragile. Any environmental interference destroys the quantum state. They need isolation from vibration, temperature changes, electromagnetic fields – everything.
Error Rates: Quantum operations have error rates that are unacceptably high for many applications. We need error correction, but that requires even more qubits.
Scalability: Going from 100 qubits to a million qubits isn’t just doing the same thing at a larger scale. New problems emerge.
Cost: These machines cost tens of millions of dollars and require specialized facilities and expertise.
But here’s the thing: these challenges are getting solved. Maybe not as fast as the hype suggests, but faster than the skeptics believe.
What You Should Do
Okay, practical advice time. What should you actually do about quantum computing and the encryption threat?
If You’re an Individual
Stay Informed: Keep an eye on quantum computing developments. When major milestones happen, you’ll hear about them.
Update Software: Use the latest security protocols and software. As quantum-safe encryption becomes available, updates will include it.
Use Strong Authentication: Two-factor authentication, biometrics, and other modern security measures add layers of protection beyond just encryption.
Don’t Panic: Your personal data probably isn’t a high-value target for quantum decryption attacks. Standard security practices are still effective.
If You’re a Business
Assess Your Risk: What data do you have that would still be valuable in 10 years if decrypted? That’s your vulnerability.
Plan Migration: Start planning your transition to post-quantum cryptography. This will take years to implement fully.
Follow NIST Standards: Use the post-quantum algorithms approved by NIST. Don’t try to invent your own.
Train Your Team: Make sure your IT and security teams understand the quantum threat and the transition plan.
Test and Prepare: Start testing post-quantum encryption in non-critical systems to understand the challenges.
If You’re in Tech
Learn the Basics: Understanding quantum computing is becoming an important skill. You don’t need a physics PhD, but you should understand the fundamentals.
Explore Quantum Programming: Tools like IBM’s Qiskit let you experiment with quantum computing now. Hands-on experience will be valuable.
Consider Career Opportunities: Quantum computing is a growing field with high demand for skilled professionals.
Common Misconceptions
Let me clear up some confusion:
Misconception 1: “Quantum computers will replace regular computers.”
No. Quantum computers are specialized tools for specific problems. Your laptop isn’t becoming obsolete. Quantum computers are terrible at most everyday computing tasks.
Misconception 2: “Quantum computing is decades away.”
For some applications, yes. For breaking encryption? Maybe less than a decade. For other uses like optimization and simulation? We’re seeing practical applications now.
Misconception 3: “There’s nothing we can do about the encryption threat.”
Wrong. Post-quantum cryptography is being developed and deployed. The threat is real, but we have solutions.
Misconception 4: “Only governments and huge corporations need to care.”
Any organization with valuable data needs to care. Small businesses, healthcare providers, legal firms – if you have data worth protecting long-term, you need a plan.
The Big Picture
Here’s what’s really happening: quantum computing represents a fundamental shift in computational capability. It’s not just faster computers – it’s computers that can solve problems classical computers fundamentally can’t.
The encryption threat is real and urgent. But it’s not hopeless. We have time to prepare and solutions being deployed.
The broader potential of quantum computing – drug discovery, AI, climate modeling, optimization – could be transformative. This technology could help solve some of humanity’s biggest challenges.
But it also creates new risks. Like any powerful technology, quantum computing can be used for good or ill.
What’s Next?
Over the next few years, expect to see:
More Quantum Breakthroughs: The pace of advancement is accelerating. We’ll see more powerful quantum computers, better error correction, and new applications.
Increased Investment: Governments and private companies are pouring billions into quantum computing. This funding will accelerate development.
Standards Adoption: Post-quantum cryptography standards will become mandatory in regulated industries. Finance, healthcare, and government will lead the transition.
Quantum-Safe Products: Software and hardware with built-in quantum-resistant encryption will become the norm.
The Arms Race: Competition between nations for quantum supremacy will intensify. This is seen as strategically important as nuclear capabilities.
New Security Threats: As quantum computing becomes more accessible, new attack vectors will emerge. The security landscape will shift dramatically.
The Bottom Line
Quantum computing is coming. It’s not science fiction anymore – it’s engineering challenges being solved in labs around the world.
The threat to current encryption is real. Organizations need to act now to prepare for a post-quantum world.
But this isn’t just about threats. Quantum computing could revolutionize medicine, science, AI, and countless other fields. The potential benefits are enormous.
The key is being prepared. Understanding the risks, planning the transition, and staying informed as the technology develops.
We’re living through a pivotal moment in computing history. The decisions made in the next few years about quantum computing and security will shape the digital landscape for decades.
My Take
I’ve been following quantum computing for years, and here’s what keeps me up at night: it’s not the technology itself, it’s the preparation gap.
Most organizations are nowhere near ready for the transition to quantum-safe encryption. They’re focused on today’s threats, not tomorrow’s.
By the time quantum computers are breaking encryption, it’ll be too late to prepare. The data will already be stolen, just waiting to be decrypted.
The time to act is now. Not because quantum computers are breaking encryption today, but because the data being stolen today will still be valuable when they do.
This isn’t alarmism. It’s reality. The quantum threat is well-documented and widely acknowledged by experts. The only debate is about timing, not whether it’ll happen.
So yeah, your passwords might be worthless soon. But more importantly, the entire foundation of digital security as we know it is about to change.
Are you ready?
Resources to Learn More
If you want to dive deeper into quantum computing, here are some solid resources:
IBM Quantum Experience: Free access to real quantum computers through the cloud. You can run experiments and learn quantum programming.
Microsoft Quantum Development Kit: Tools and resources for quantum computing development.
NIST Post-Quantum Cryptography: Official documentation on quantum-safe encryption standards.
Quantum Computing Report: Industry news and analysis on quantum computing developments.
“Quantum Computing for Everyone” by Chris Bernhardt: Great introductory book that explains concepts without heavy math.
MIT OpenCourseWare: Free quantum computing courses from one of the world’s leading institutions.
Final Thoughts
Look, I get it. Quantum computing sounds complicated and distant. It’s easy to think “I’ll worry about it when it becomes a problem.”
But that’s exactly the wrong approach. By the time it’s an obvious problem, it’s too late to solve it.
The organizations and individuals who take quantum threats seriously now will be protected. The ones who wait will be vulnerable.
You don’t need to become a quantum physicist. You just need to understand the basics, stay informed, and make sure the systems you rely on are preparing for this transition.
The quantum future is coming whether we’re ready or not. The only question is: will you be prepared?
What do you think? Are you concerned about quantum computing and encryption, or does it seem too far away to worry about? Drop your thoughts in the comments – I’m curious what people think about this.
Keywords: quantum computing, quantum computers, post-quantum cryptography, cybersecurity 2025, encryption security, quantum threats, qubits, quantum algorithms, data security, cyber threats, quantum supremacy, NIST standards, quantum key distribution, harvest now decrypt later, quantum computing explained